Why “Bolt-On” Privacy Breaks Momentum
The Cost of Reactive Privacy Many organizations still treat privacy as something to add on later – scripts, manual exceptions, or patches that meet compliance requirements but rarely strengthen long-term governance. This “bolt‑on” approach might work temporarily, but it creates structural weaknesses that slow development and undercut trust. As discussed in Privacy by Design: The AI Podcast, Episode 2 – What It Takes to Build a Privacy‑First AI Product, reactive privacy programs often lead to bottlenecks, frustrated teams, and a compliance posture no one actually respects. At one UK bank, for example, it took six months for developers to gain permission to access protected data. To get their work done, most filed exceptions that bypassed controls. Over time, adoption of “the rules” fell to near zero, a cautionary tale of what happens when privacy is treated as an afterthought rather than a design principle. Building Privacy Into the AI Solution A privacy‑first model looks very different. Instead of relying on gatekeeping and approvals, strong programs automate privacy controls at the platform level. They ensure that the “secure path” is also the fastest and easiest for developers. This shift turns compliance into an enabler, not an obstacle. Teams that document both how and why privacy decisions are made can sustain momentum through staff turnover, regulatory shifts, and even rapid AI model evolution. Privacy, in other words, stops being “compliance overhead” and becomes part of the development process itself. The Role of AI in Strengthening Governance AI can help scale and enhance privacy‑first development by automating risk detection, surfacing policy recommendations, and streamlining repetitive workflows. Automation ensures consistency across teams while reducing the manual overhead that slows deployment. However, AI does not, and should not, replace design and governance principles. Human oversight defines the boundaries, ensuring automation serves the organization’s values and ethics. The strongest programs blend both elements to create lasting resilience. Privacy and Performance Can Coexist Organizations that integrate privacy from day one gain the dual advantage of speed and trust. Instead of trading one for the other, they build systems that evolve confidently alongside regulatory and technological change. That’s what Episode 2 of Privacy by Design: The AI Podcast explores in depth: how privacy‑first AI development helps teams move faster, lower risk, and stay ready for whatever comes next. Listen to the full episode: Listen Here A Guide to Smarter Data Privacy: Building AI with Trusted Data Safe AI isn’t just a step you add at the end. It’s a discipline you build into how data flows. This playbook shows security, data, and ML leaders how to one, keep a live map of sensitive data, two, apply proportional protections before training or indexing, and three, generate audit evidence automatically so you ship faster, with lower risk and fewer rework cycles. What you’ll get: a live sensitive-data landscape, enforceable pipeline gates, and a simple scorecard to prove quality and compliance. Data Privacy Guide
Privacy as a Market Accelerator

Case Study A top New York financial firm turned their privacy-first strategy into a competitive win. Facing increased demand for strong data protection from European clients, the firm invested in proactive privacy measures—implementing advanced tokenization and transparent processes across operations. Rather than view privacy as a compliance hurdle, they used it to unlock new opportunities. By positioning privacy at the heart of their offerings, the firm gained access to $1–2 billion in new EU business, far outpacing peers who saw privacy as just legal box-checking. The strategy created not only regulatory confidence but tangible business growth, lowering IT overhead, reducing risk, and earning customer trust that opened entirely new markets. This real-world result shows privacy-first practices fuel business expansion and bottom-line impact—not just compliance. This transformation was spearheaded by Mike and George, whose deep experience in technology and data security empowered the firm to innovate and deliver market-leading solutions. Today, they channel these insights into C2 Data Privacy Platform, where their focus is on building best-in-class DSPM, powered by AI, giving clients smarter, more scalable privacy management than legacy RegEx-based tools. Their leadership and vision ensure privacy not only drives compliance but creates true market advantage. Highlights Billions in New Revenue: Privacy-first strategy enabled the firm to access $1–2 billion in EU business without opening a physical facility in Europe. Tech Expertise: Advanced privacy measures, like tokenization and transparency, met client and regulatory expectations remotely. Cost Savings: The approach saved costs, avoided local infrastructure, and created a major competitive advantage for global market entry.
Smarter Privacy: The Hidden Accelerator in AI Application Development

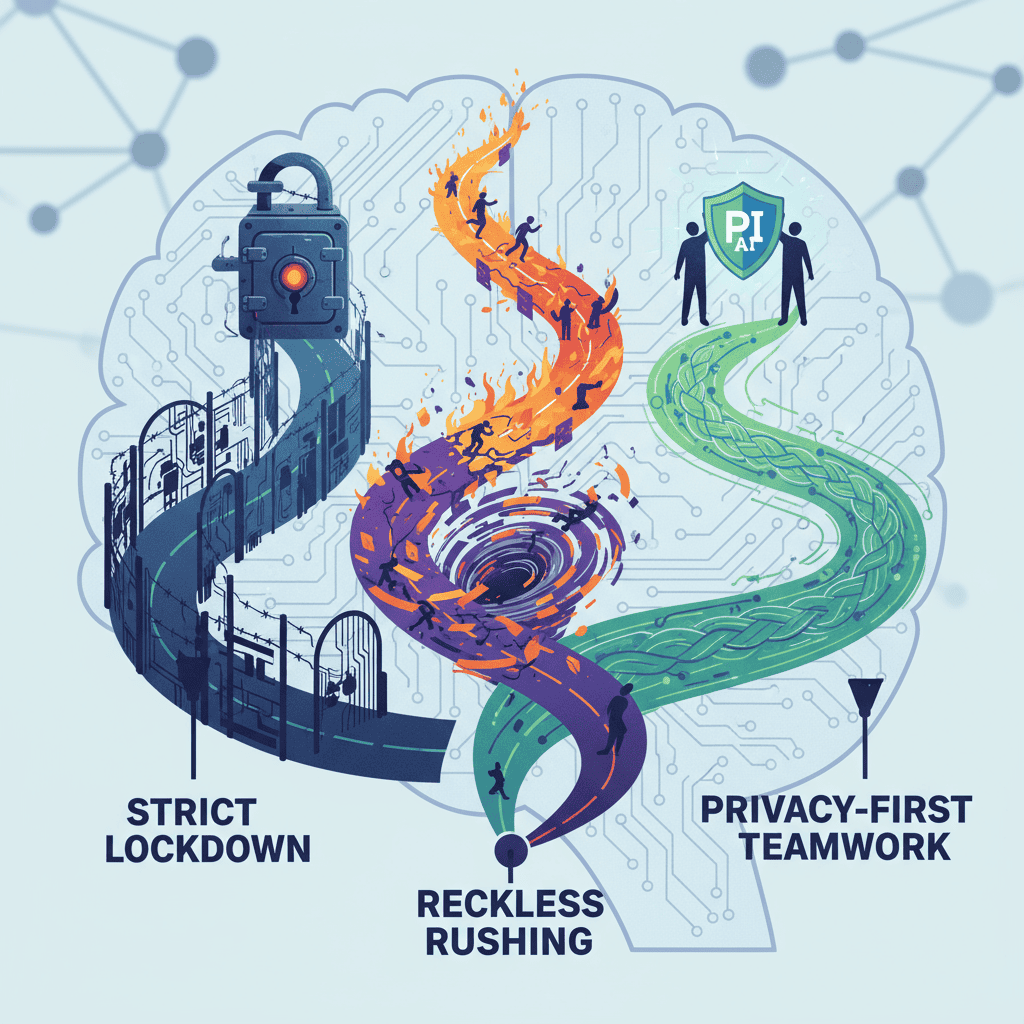
The old tech adage “move fast and break things” is showing its limits in the age of AI. In data-driven application development, rushing without embedding privacy can create a minefield. This triggers a pendulum swing between over-locking all data or flinging open the gates in the name of speed. Locking everything down stifles innovation and frustrates teams, while going too fast can expose companies to breaches and regulatory blowback, both resulting in wasted money, compliance headaches, and lost momentum. But there’s a smarter way. Embedding privacy across the board. Embedding privacy at every stage, especially with automated data discovery and classification changes the risk equation. Instead of treating privacy as a roadblock, organizations can transform it into an operational advantage. As described by experts George and Mike in their recent podcast, teams that invest up front in automated data mapping and classification scale responsibly, avoid brittle models, and steer clear of expensive, patchwork fixes later. The “privacy-first” approach allows developers to ship applications with agility, unburdened by constant exception processes or late-stage panic about compliance, even as regulations evolve. Critically, this isn’t just about ticking boxes for compliance. When privacy is woven into the developer experience, teams are liberated to create, iterate, and deliver with confidence. Adopting automated discovery tools doesn’t just reduce hidden organizational costs; it establishes a culture where creativity thrives, technical debt is minimized, and customer trust is never an afterthought.
A Guide to Smarter Data Privacy: Building AI with Trusted Data

Smarter Data Privacy Is Not Just Software Safe AI isn’t just a step you add at the end. It’s a discipline you build into how data flows. This playbook shows security, data, and ML leaders how to one, keep a live map of sensitive data, two, apply proportional protections before training or indexing, and three, generate audit evidence automatically so you ship faster, with lower risk and fewer rework cycles. What you’ll get: a live sensitive-data landscape, enforceable pipeline gates, and a simple scorecard to prove quality and compliance. Step 1: Assignment, Alignment, Consent Make privacy a shared responsibility with clear ownership and update consent for AI use. Smarter data privacy starts with culture, not code. Leadership, engineering, and compliance align on privacy by design when someone owns outcomes. Without a named lead, efforts fragment and get ignored under deadline pressure. As AI products reach customers and patients, the privacy lead should partner with counsel to include AI modeling in consent. Actions: Designate or confirm a single accountable owner for data privacy across acquisition, discovery, and AI use. Empower them to manage shadow data, enforce safe data practices, and engage external experts when needed. Review data usage consent with counsel and add clear AI language. Example Language: “We may use your information to improve the AI models that power [feature]. We apply de-identification and strict access controls, and we do not use your data to train models shared outside [Company] without your permission. You can opt out anytime in [settings].” Step 2: Modernize Data Discovery Continuously identify PII/PHI data across your environment. Data is the hardest part of AI. You cannot protect what you cannot see, and plugging into an LLM will not work until you know what sits in databases, notes, emails, and logs. Discovery is not a one off. If it is not ongoing and automated, sensitive data slips into pipelines unnoticed. Use AI to start faster, then finish with disciplined review and quality controls. Actions: Select a contextual and semantic discovery solution that inspects content (not just column names or simple regex). Build a baseline sensitive-data landscape across priority sources; capture what/where/how much/first-seen/last-seen. Schedule scans and assign source owners; track coverage percentage and freshness in a simple dashboard. Add parsers for free text, JSON, logs, and files to close blind spots. Log findings to an audit trail (source, field, entity, confidence, action taken). Deliverable: Complete coverage, fresh dashboard, and the first “live landscape”. Step 3: Evaluate Classification and Risk Profiling Capabilities Classify PII and PHI with context and rank risk to keep a live landscape, not a static catalog. Sensitivity changes with exposure, regulatory duty, and business impact. Shallow or stale classification over-protects low-risk data and under-protects critical fields. By “introspect the data,” we mean the system inspects values and their context—patterns, neighbors, and linkers (e.g., device IDs, store IDs, timestamps)—to infer type and risk so that controls are applied where they matter most. Actions: Validate accuracy with tiered thresholds on your data Build a labeled set (≈100–200 examples per high-priority entity) across structured tables, unstructured text, and JSON/logs; include edge cases, look-alikes, and linkers (e.g., device/store IDs). Measure per entity precision, recall, F1, plus 5–10 example hits/misses by source type; record confidence scores for review cutoffs. Set use-case targets exactly as above (Tier-1 ≥0.95–0.98 F1; logs/support ≥0.90; triage 0.80–0.90). Stand up a lightweight review loop: 48-hour SLA; record system label → reviewer label, reason, severity, and location; update rules/patterns monthly and re-run the sample to verify lift (keep a simple changelog). Quick QA guardrails: hold out ~20% for validation; zero known Tier-1 misses; cap Tier-1 FPs to protect reviewer bandwidth. Deliverable: A one-page scorecard (thresholds, scores by entity/source, top misses, actions taken). Stand up a reviewer workflow & correction queue Create a simple “review needed” queue (Jira/Asana/sheet) for edge cases; assign an owner + SLA; capture snippet, system label → reviewer label, reason, severity, location. Roll recurring misses into updated rules/patterns and keep a changelog. This boosts quality without over-promising full automation. Step 4: Secure Data Protect the data before you train the model or index. Discovery and classification only matter if you act on them. Securing data means fit-for-purpose controls by use case: synthetic data for safe model training, pseudonymization/de-identification for analytics, tokenization or format-preserving encryption when formats must be retained, and anonymization when reversibility must be impossible. If data isn’t secured upstream, risk flows into training corpora, embeddings/vector stores, and logs—becoming exponentially harder (or impossible) to remediate. Early action reduces liability, limits rework, and accelerates safe scaling. Actions: 1. Map Controls to Use Cases – Start Small, then Scale Review your de-identification toolkit and map each control to a single pilot pipeline first (masking, redaction, tokenization/FPE*, encryption*, synthetic data). Because PII/PHI is classified in context, reserve the heaviest protections for Tier-1 data and lighter controls where risk is demonstrably lower, conserving resources and speeding delivery. 2. Enforce Security Gates in the Pipeline Gate A (ingestion): scan → label → auto-apply control → log decision. Gate B (pre-train/index): Block if any Tier-1 remains; allow override only with justification and auto-audit. 3. Unify Discovery, Security, and Monitoring Use (or integrate to) C2 to enforce protections and policies end-to-end with policy-as-code at ingestion and pre-training/index checkpoints, plus centralized audit/evidence packs and alerting. Step 5: Govern Data Build oversight into everyday workflows for data insights. Data is always changing. Governance sticks when it’s automated. Use policy-as-code gates so every scan, decision, and override is written to the audit log. Maintain a live landscape with scheduled scans and clear ownership. Monitor new exposures, keep an exception register with SLAs, and generate evidence packs from the audit log, no separate audit projects required. Deliverable: Monthly evidence pack (HIPAA/GDPR), exception register, policy rules repo. Actions: Discovery gates at ingestion & pre-train/index: Scan every dataset; auto-apply masking/de-identification as required; block pre-train/index if Tier-1 remains; record decisions and overrides in the audit log. Maintain a live sensitive-data landscape: Keep the landscape current across priority sources with scheduled scans and clear ownership per source; track coverage and freshness
Next-Gen AI Privacy: From Compliance to Competitive Advantage
Three Paths to AI Privacy – Lockdown, Caution to the Wind, or the Smart Choice What are your real options when launching AI with sensitive data? Most teams run into three choices: lock privacy down to a crawl, rush ahead and ignore it, or embed privacy from the start. Locking down stifles progress and teams get frustrated, give up, or detour around controls. Ignoring privacy speeds short-term but leads to abandonment or risky outsourcing down the line. The smarter way is a privacy-first path built on smart discovery, classification, and remediation accelerating safe launches, preventing brittle models, and setting up for long-term resilience. How can privacy by design boost speed and confidence?By weaving privacy into processes from day one, technical debt shrinks and creative teams stay empowered. Smarter discovery and remediation mean no more ugly “aftermarket” patches. Winning teams move fast and stay compliant without betting the business. The Hidden Cost of Privacy Shortcuts—What’s Draining Your ROI? How do privacy missteps show up in the budget and timeline? Copying strict production controls everywhere inflates IT costs—sometimes 4–10X —while restricting data access slows creative work. Overly tight policies starve most of the team, so shortcuts creep in; risk and technical debt quietly multiply. What’s the fallout from poor discovery and tracking?Unchecked, data “drift” leads to forgotten backups, vendor leaks, and legal headaches. Real stories show: once sensitive information escapes, contracts can’t fix reputational or financial damage. Early, ongoing discovery and classification close the gaps—so exposure is never a surprise. AI Privacy Myths – Does Protection Really Slow Performance? Will privacy actually delay AI model development or accuracy? Only if it’s an afterthought. Guests share: with reusable pipelines and automated masking, data refreshes that once took over a day now take just an hour. Developers get compliant, masked data fast—every morning, not mid-afternoon. Is it cheaper to bolt on privacy later?Never. Fixing mistakes or remediating breaches is costlier than “doing it right once.” Modern tools and process orchestration let privacy and velocity run in parallel—empowering teams without compromises. Building Lasting AI Privacy—How Do Governance, Culture, and Customers Shape the Future? What future-proofs your AI privacy strategy as regulations and customer demands evolve? Laws like the EU AI Act are raising requirements, but real-world winners start early and stay agile. Continuous discovery, classification, and platform-level automation make privacy lasting and adaptable, not a fragile, bolt-on patch. How do customer expectations drive business value?A case from the podcast: a NY financial firm opened $1–2B in new EU business—not by legal mandate, but because customers demanded privacy-first solutions. Tokenization and process transparency unlocked growth, showing that privacy now fuels opportunity, not just compliance.
From Chaos to Confidence: How Smart Data Privacy Transforms Healthcare
Key Takeaways Continuous discovery of PHI/PII data transforms healthcare privacy from chaos into clarity. Automated, purpose-driven controls replace manual processes and reduce risk. Precision in protection (masking, tokenization, encryption, redaction) accelerates safe innovation. Automation enables rapid delivery of compliant, self-service datasets, supporting both care and research. Patients and clinicians benefit from trust, speed, and fewer barriers throughout the data lifecycle. Smarter data privacy is not a barrier; it’s a catalyst for progress in modern healthcare. Every day, patients, clinicians, and IT specialists witness the delicate balance between using data to improve care and safeguarding that same information from misuse. At each touchpoint—from a scheduled appointment to a new system update—there is an ever-present need to keep personal health details safe while ensuring care teams have the right insights, right when they need them. Progress starts with a clear map of where PHI/PII data lives – a sensitive data landscape. Many healthcare organizations are surprised to find protected health information hiding in backup drives, handwritten notes, and overlooked database fields. Building this living inventory empowers teams to move from guesswork to proactive risk reduction. Visibility is the first step toward trust. Once organizations understand where personal and health information resides, they can transform static privacy policies into dynamic, real-world safeguards. Consent rules are no longer theoretical. Instead, they work behind the scenes—automatically granting or restricting access for specific patient profiles, diagnosis categories, or research use cases. The real advantage comes when privacy controls are tailored to the task. Instead of locking everything down or leaving too much open, teams select the right level of safeguarding. Creating test data for a new patient portal? Mask real identities with lifelike, anonymized details. Supporting a research study? Apply tokenization to allow necessary reversibility—tightly audited and controlled. Encrypt records in storage and in motion, ensuring that even system integrations and analytics pipelines reinforce privacy. With precision protection, innovation happens faster because everyone has confidence in the process. Automation is the unsung hero. No one has time for delays caused by repetitive privacy checklists or ticket backlogs. Automated detection and risk-scoring keep privacy ahead of the curve, flagging new PHI instantly and generating compliance reports on demand. This means clinicians, data analysts, and app builders spend more time helping patients and less time waiting for access or review. The proof is in the outcomes: EHR upgrades ship as scheduled, patient trust grows, and analysts drive new discoveries with purpose-built datasets. Every stakeholder—from front desk staff to the C-suite—knows that privacy is more than a checklist; it’s a living advantage for the entire healthcare enterprise. Frequently Asked Questions 1. What does “privacy-first AI” actually mean? Designing AI systems so privacy constraints—discovery, consent, minimization, and security—are built into the data lifecycle from the start, not bolted on later. 2. Why start with discovery? You can’t protect what you can’t see. Discovery reveals hidden PII/PHI and data sprawl so you can prioritize controls and avoid training on sensitive data by accident. 3. Isn’t privacy-first slower? Done right, it’s faster. You avoid rework, brittle models, and blocked launches caused by late-stage privacy issues. 4. What’s the difference between de-identification and anonymization? De-identification removes or transforms identifiers but may remain re-linkable in context. Anonymization aims to prevent re-identification even with external data harder to achieve and usually with utility trade-offs. 5. What is “purpose and consent” in practice? Document the lawful basis, intended use, allowed recipients, retention, and jurisdictions; then enforce those rules at data gates and log evidence.
Fix Privacy Upstream: How to Keep AI from Learning What It Shouldn’t

The Blind Spots Haven’t Disappeared PII and PHI rarely sit neatly in columns. They leak into emails, tickets, chat logs, free-text notes, forgotten backups, and shadow exports. Even with strict policies and masking, gaps remain. And “linkers” like timestamps, device IDs, and store numbers can quietly re-identify people. AI Multiplies the Blast Radius When unprotected data feeds a model, it isn’t just stored, it’s learned. Patterns you never meant to expose can resurface in outputs or embeddings. Once sensitive data is in the weights, you can’t simply delete it. Shortcuts tolerated in legacy systems become accelerants for risk in AI. What “Smarter Privacy” Looks Like Discover everywhere. Go beyond schemas to scan free text, files, logs, and vector stores. Classify with context. Identify obvious identifiers and the linkers that stitch identities back together. Enforce consent at ingestion. Track purpose, scope, and retention—and block out-of-policy uses. Hold the line at model boundaries. Keep raw fields on the safe side of embedding/retrieval. Monitor continuously. Validate inputs and filter outputs before they reach users. Guardrails for the Pipeline Inventory & map: Find PII/PHI across data stores, notes, and backups. Rank sensitivity & impact: Prioritize what the model can safely see. Neutralize linkers: Tokenize, mask, or drop fields that enable re-ID. Consent & lineage: Bind datasets to purpose and prove you’re allowed to use them. Pre-train review: Block risky fields before training or indexing. Runtime filters: Add output checks to prevent unintended disclosure. AI amplifies every oversight. Fix privacy at the source and you can move fast—without creating tomorrow’s breach.
Data Privacy in the AI World
Podcast Why Data Masking Isn’t Enough for AI Pipelines Data masking looks good on a checklist. It satisfies the “something was done” mentality. But in today’s AI pipelines, masking isn’t real protection. If we want smarter data privacy, we have to assume someone—whether it’s a motivated insider, a researcher, or even an AI model itself—can stitch the pieces back together. I was recently interviewed for a Techopedia article about the M&S hack. The official line was that “no payment data was stolen.” But here’s the problem: attackers don’t need credit cards to hurt you. Customer records, account details, system notes, those can be just as damaging. The same logic applies to AI. Mask a dataset all you want, but if context and linkages remain, inference risk will find a way to expose what you thought was hidden. I’ve seen how quickly weak masking falls apart. Correlating timestamps, receipt numbers, or IDs against public breadcrumbs is often enough to reverse so-called “protected” data. That was before AI was widely available to spot patterns at scale. If you’re relying on masking alone to safeguard PII in financial services or PHI in healthcare AI systems, you’re betting against math—and you’ll lose. Smarter data privacy means building resilience, not illusions: Irreversibility first. Shuffling or reversible tokenization doesn’t cut it. Strong tokenization and encryption are the baseline. Context matters. Semantic data discovery and governance for AI pipelines must surface subtle identifiers—timestamps, IDs, system codes—that attackers love to exploit. Proof over promises. Continuous testing and AI audit and monitoring should be part of release cycles. If you can’t demonstrate compliance, you don’t have it. This is where regulation is heading—the EU AI Act will force organizations to prove they can prevent PII leakage in AI model training. Customers are already demanding it. They don’t want promises; they want evidence. In our new podcast, Privacy by Design: The AI Podcast, George Barroso, Kris Glover and I talk about the importance of taking the appropriate first step in AI development. I invite you to listen and connect with us to talk about your own AI development and the ways in which you can put data privacy at the front of your development. AI development is moving at full speed, but privacy can’t be bolted on later. The good news is with the right tools smarter privacy makes it possible to innovate quickly without handing adversaries an easy hack. Masking might tick a box. Smarter privacy earns trust.
AI in Healthcare: Protecting Patients, Accelerating Progress
Listen to the Podcast Introduction: Clinical Data, AI, and Patient Trust Few industries handle data as sensitive as your healthcare data. Patient records, lab results, insurance claims, and clinical notes reveal deeply personal details. Regulations like HIPAA have long enforced protections, but with AI now increasingly at the forefront, safeguarding PII and PHI is more critical than ever. Clinical data, when responsibly used, empowers AI to detect disease earlier, personalize treatments, optimize care coordination, and ultimately save lives. But leaning into AI without proper privacy measures risks leaking sensitive information either through direct exposure or through inference risk. Once PHI is absorbed into a model’s weights, it cannot simply be deleted. Retraining is the only path costly, time-consuming, and slows innovation. The path forward in healthcare is clear: audit the data from the start, embed privacy in design with continuous semantic discovery, and move safely at speed. The Three Roads Every Healthcare AI Development Team Faces Healthcare teams often consider three paths some are quicker than others, but only one is truly responsible: Overprotect and stall. Freezing access to all data reduces risk but delays models that could detect radiology abnormalities or predict readmissions. Time lost here is time patients wait. Shortcut and hope. Using unreviewed or live patient data may speed pilots, but in healthcare where HIPAA compliance and patient trust are paramount, it’s a legal and ethical minefield. Even seemingly trivial shortcuts like pulling production data without full de-identification vs anonymization can lead to major violations.¹ Smarter privacy. The sustainable path. Start with discovery, apply contextual protections, enforce consent rules, and provision safe datasets rapidly. It’s both fast and compliant. Only the third option achieves innovation and responsibility. Why Data Discovery Matters for Healthcare AI Compliance Clinical datasets are vast and fragmented spanning EHRs, imaging systems, notes, backups, and logs. Masking or policy-only protection is insufficient unless you know what’s there. Without discovery, PHI may slip into training data, triggering liability and expensive retraining. With semantic discovery, every data source gets mapped, consent-tagged, and risk-scored so AI teams can train without exposing identities. Discovery isn’t just risk mitigation; it’s what unlocks safe AI innovation. Common Privacy Failure Modes in Healthcare AI Models AI initiatives often fail in familiar patterns: Direct leaks. Identifiers like MRNs or claims data get baked into model weights. Inference risk. Seemingly benign fields like timestamps or location codes may be combined with external data, revealing identities. Weak masking. Shuffle-based obfuscation maintains patterns that can be reversed. Exception creep. Live data used temporarily in test environments becomes part of long-term pipelines—and eventually, part of launched models. These practices undermine AI compliance and trust—but all are preventable with discovery-first approaches. Healthcare Privacy Failures in the Real World These real-world cases show how fragile PHI is when governance falls short: AI Chatbot Misconfiguration (U.S. Hospital): An AI-powered scheduling tool leaked sensitive patient details to third-party analytics—without consent. A textbook HIPAA violation highlighting how fast privacy can break.² Imaging Center Cloud Breach: A misconfigured cloud environment exposed patient names and diagnostic imaging, revealing how unsecured AI data pipelines can backfire.² Therapy Records Exposed: Confidant Health, a virtual mental health provider, accidentally exposed over 120,000 files and 1.7 million logs—including session transcripts and videos—via an unsecured database.³ Psychotherapy Notes Extortion (Finland): The Vastaamo clinic data breach leaked session records from ~30,000 patients who were then individually extorted. The attack triggered legislative improvements in data protection.⁴ Lessons: Misconfigurations within AI systems can rapidly expose PHI. Without semantic data discovery, sensitive information lurks undetected in backup logs or unstructured fields. Weak protections fail under scrutiny. Ongoing monitoring is crucial to catch PHI before it’s exploited. Discovery-first privacy isn’t just best practice it’s about safely innovating for the future. Healthcare AI Data Compliance Best Practices: Smarter Controls for PHI Strong AI needs smart privacy: Continuous semantic discovery. Scan across EHRs, notes, imaging, and backups. Consent management workflows. Ensure treatment vs. training use is clearly defined. Context-aware protection. Use irreversible transforms and reduce precision on linkers. AI audit and monitoring. Detect PHI exposure before it hits outputs. Self-service safe data. Enable researchers with compliant datasets instantly. The safe path becomes the smoothest path when privacy is embedded in design. Conclusion: Data Privacy as the Foundation of Healthcare AI Innovation Clinical data is both incredibly valuable and deeply sensitive. Mishandled, AI becomes a threat. Protected with data discovery-first, consent-aware architecture, AI becomes a healer. Responsible AI governance is not an obstacle, it’s the foundation for accelerating safe, transformational healthcare technology. The best time to secure PHI in AI was before development. The second-best time is now. References Kanter G. AI chatbots and HIPAA risks in healthcare. USC Price Post. July 2023. Holt D. HIPAA violations in the AI era: Real-world cases and lessons learned. DJ Holt Law. February 2025. Fowler J. Therapy sessions exposed due to unsecured database at Confidant Health. Wired. Sept 2024. Ralston R. Vastaamo psychotherapy breach case study. NIH PMC. 2024.
Preventing PII/PHI in AI Model Training

Listen to the Podcast Responsible AI Starts with Trusted Data AI is moving fast. New models launch every week. But if personally identifiable information (PII) or protected health information (PHI) slips into your training data, your system can resurface it later — directly or through inference. Fixing that after the fact is slow, costly, and puts compliance at risk. Old Problems, Higher Stakes Organizations still struggle to answer basic data governance questions: What data do we have? Where did it come from? Who can use it? Decades of exports, backups, and free-text fields create blind spots. Feeding large language models (LLMs) directly from those lakes is how privacy failures become breach timelines. Like SQL injection taught us, raw inputs can’t be trusted. AI pipelines need data governance from ingestion to inference. Why Masking Isn’t Enough Traditional masking swaps identifiers, but timestamps, device IDs, or location linkers can still re-identify people. Responsible AI requires context-aware, semantic data discovery to prevent “anonymous” data from becoming obvious. Discovery Comes First Regex isn’t enough. “Brown” might be a color or a last name. Effective discovery must be: Continuous — not one-time scans. Semantic — understanding context. Governance-driven — tracking purpose and consent. Data collected for service delivery does not automatically grant rights to train AI models. Responsible AI pipelines must embed these checks from the start. The Fast Path to Compliance & Delivery Teams often skip privacy controls because they slow projects down. The solution: make discovery and enforcement the default — and faster than the workaround. With C2 Data Technology: Discovery and consent are embedded in the flow. Sensitive data is safe to use in minutes, not weeks. Conclusion You shouldn’t have to choose between compliance and innovation. Responsible AI starts with trusted data. Build governance into the pipeline, prevent PII/PHI from entering training data, and ensure your models ship fast — and stay safe. For more insights, listen to Episode 1 of our podcast, “Privacy by Design: Responsible AI Starts With Trusted Data.”
Responsible AI in Financial Services | Data Privacy & Discovery

Responsible AI in Financial Services The financial services industry has always been built on trust. Customers hand over their most sensitive information — from Social Security numbers and account balances to transaction histories and sometimes health-related data — with the expectation that it will be safeguarded. As banks, insurers, fintechs, and wealth managers accelerate adoption of AI in financial services, that expectation has never been more fragile. AI promises faster fraud detection, smarter underwriting, personalized wealth management, and real-time customer service. But AI also learns from whatever data it’s given. If PII or PHI is pulled into training or inference without discovery and protection, those details can resurface in unexpected ways — sometimes directly, sometimes through inference risk (also called model inversion or re-identification). Unlike traditional systems, once data is absorbed into a model’s weights, it cannot simply be deleted. Retrofitting privacy after the fact means retraining from scratch — a costly and time-consuming process. This paper argues that responsible, trustworthy AI in financial services begins not with the model, but with how institutions map, classify, and govern their data from the start. AI Development in Financial Services: Three Paths for PII/PHI Privacy Financial institutions embarking on AI projects typically face three choices: Option 1: Lock Down Everything Restrict access to all data until it has been exhaustively reviewed. This minimizes risk but slows development to a crawl. In fast-moving markets, even a few months’ delay can erase competitive advantage. Option 2: Ignore the Risks Some teams move fast, wiring unreviewed data lakes into models or pulling production data into test environments. This accelerates delivery but creates exposure to regulatory fines, reputational damage, and privacy breaches. Option 3: Take the Smarter Path Begin with data discovery (also called data mapping or sensitive data identification), protect PII/PHI, enforce purpose and consent, and provision compliant data quickly. This approach allows teams to deliver fast without gambling on shortcuts that become liabilities. Responsible AI is about making the third option — privacy-first AI development — the natural and fastest path. Responsible AI in Finance: Data Discovery and Governance for Readiness Financial institutions carry an outsized duty of care. Regulators demand AI compliance and oversight, insurers assess controls before underwriting cyber and privacy risk, and institutional clients demand contractual assurances. Consumer trust is fragile: one breach can erase decades of brand equity. Transparency in Financial AI Systems Every dataset’s origin, lineage, and purpose are documented. Consent and Purpose in Data Use Data collected for one purpose isn’t silently reused for another. Training rights ≠ inference rights. Output Control and Accountability Outputs are filtered to prevent sensitive details from being echoed back, with audit trails ready for regulators and partners. AI Privacy Risks: How Financial Models Fail Without Data Discovery Neglecting AI data privacy leads to recurring failure modes: Direct Leakage of Identifiers Social Security numbers, account details, or claims data absorbed into model training. Linker-Based Re-Identification and Inference Risk Harmless-looking fields like branch ID, device ID, or transaction time can combine with external data (such as receipt photos on social media) to reconstruct customer histories. Reversible Transformations Shuffled IDs or token swaps preserve underlying patterns and can be undone quickly. Purpose Drift and Exception Creep Data collected for one purpose reused without consent, or “temporary” exceptions to use production data that become permanent. The Cost of Ignoring AI Data Privacy in Financial Services In financial services, failures in AI privacy don’t just create technical debt — they trigger business impact: Regulatory fines under GDPR, CCPA, GLBA, NYDFS, or OCC. Model risk management findings that halt projects or force retraining. Higher cyber/privacy insurance premiums or outright denial of coverage. Customer trust erosion, leading to churn and reputational damage amplified by the press. The hidden cost is time. Every week lost to cleanup or retraining is a week of missed competitive advantage. Discovery-First AI Privacy Controls for Banking and Insurance The smarter path is not “more controls everywhere” — it’s smarter controls: Discovery-First Data Mapping Continuously scan CRMs, call transcripts, claims notes, and backups for PII/PHI. Go beyond regex with semantic, context-aware discovery to capture linkers and free-text fields. Purpose and Consent Registry Tag datasets with approved uses. Distinguish training rights from inference rights. Block “do not use” data at ingestion. Context-Aware Protections Apply irreversible transforms to identifiers. Reduce precision on time, geo, or device data to neutralize re-ID risks. Output Filtering Catch sensitive data patterns before they reach customers or regulators. Automated Provisioning Provision compliant, risk-scored datasets instantly for developers and analysts. Make the safe path the fastest path. Who Needs Protected Data in Finance? CISOs, Risk Teams, and Data Scientists Within a financial services firm, different roles have different needs: CISOs and Chief Privacy Officers Need audit-ready evidence of discovery and protection. Compliance and Model Risk Teams Require clarity on training vs inference rights, with controls documented for regulators. Data Scientists and Machine Learning Engineers Want fast, self-service access to privacy-safe data that won’t derail projects later. Business Line Leaders Need confidence that AI will scale without reputational or regulatory backlash. Partners, Vendors, and Insurers Demand contractual proof that data privacy and AI governance frameworks are enforced end-to-end. Building Trustworthy AI in Financial Services with Discovery-First Privacy Financial services organizations cannot afford to treat AI data privacy as an afterthought. The risks — regulatory, reputational, financial — are too great. But locking everything down isn’t the answer either. The future belongs to firms that make privacy the fastest path: discovery-first, consent-aware, context-driven protections that enable responsible, ethical AI to move at the speed of the market without becoming a liability. The best time to prepare was before AI. The second-best time is now.
C2 Data Technology’s Mike Logan Talks “Low-Risk” Data in Techopedia
Marks & Spencer Data Breach: A Wake-Up Call for Companies and Consumers Data breaches are often framed as isolated incidents, but they reveal deeper systemic issues in how companies protect sensitive information. The recent M&S breach, which compromised customer data but not payment details, is a case in point. While the retailer has been transparent about the attack, security experts including Mike Logan, CEO of C2 Data Technology, caution that even so-called “low-risk” data can pose significant threats. As Logan explains, “Attackers excel at piecing together small, seemingly harmless data points to reveal much more sensitive information.” This kind of inference attack can turn a few exposed details into a much larger threat, exploiting trust to gain further access. For a deeper dive into what this means for companies and consumers, including practical steps to stay safe, check out the full article. M&S Hack Warning: Why Your “Low-Risk” Data Is Still a Big Risk
CEO Mike Logan Discusses How Startups Should Protect Their Data in TechRound

“In their data protection strategies, small businesses and start-ups should prioritise preparing against AI-Driven Attacks: Organisations need to bear in mind that while AI and Machine Learning will create new opportunities for efficiencies and ways of working, they’re doing the same for cybercriminals. AI and Machine Learning use in cyber-attacks has been on the increase in 2025. Smaller businesses are even more vulnerable, so it’s important for data privacy programmes to be kept up to date so they can respond quickly to new threats. Deepfake phishing and adaptive malware are examples of sophisticated attacks that are now being employed to target organisations faster and more easily. Businesses will need to anticipate these evolving threats by implementing advanced AI-driven cybersecurity measures. Recommendations 1. “Audit your organisation’s technology. Are you using technology designed for today’s challenges? Security by obscurity will no longer work in today’s interconnected business environment. By the same token, yesterday’s technology will not help your organisation respond to the evolving and complex cybersecurity challenges of today, 2025, or 2030. To protect your organisation, it’s critical that you employ data privacy solutions that are addressing the evolution of cybercrime and have robust roadmaps that proactively prevent data breaches from happening in the first place, rather than just reacting to them. 2. “Ask for help! Automation and AI can help fill the skills gap in your organisation, use it. If your team is not prepared to take on the new challenges that data security presents, don’t risk it. Work with trusted experts who build solutions that can reduce your risk, remove manual efforts, and scale with your organisation. Automate, automate, automate… 3. “Always be evolving. You know your business better than anybody so it is up to your organisation to move along data privacy maturity curve as fast as possible. The more your organisation knows and understands the better positioned your company will be to face the data security challenges ahead.” Read the Full Article
Shadow Data: The Hidden Threat to Your Organization’s Security

In the digital age, data is the foundation for most businesses. However, not all data is managed effectively. A hidden risk that often goes unnoticed is shadow data. This unmanaged and unmonitored data can create significant vulnerabilities for businesses. Let’s explore what shadow data is, why it’s dangerous, and how organizations can address it effectively. What Is Shadow Data? Shadow data refers to any organizational data that exists outside of your company’s approved IT systems or governance framework. This could include files stored on personal devices, data shared through unauthorized cloud services, or forgotten backups left in unmonitored environments. Essentially, it’s the data that slips through the cracks of your formal IT policies. Shadow data often arises from well-meaning actions, such as: A developer copying sensitive production data into a testing environment and forgetting to delete it. Employees sharing files using unsanctioned collaboration tools for convenience. Legacy systems or old backups containing sensitive information that no one remembers. While these actions may seem harmless, they create a growing pool of unmanaged data that is invisible to IT teams—and that’s where the danger lies. Why Is Shadow Data Dangerous? Shadow data poses several risks that can have serious consequences for your organization: 1. Security Vulnerabilities Since hidden data isn’t monitored or secured like official data, it becomes an easy target for cybercriminals, potentially leading to breaches of sensitive information. 2. Compliance Risks Many industries are governed by strict regulations regarding data privacy and security. Shadow data often exists outside these controls, putting your organization at risk of non-compliance and resulting in fines and reputational damage. 3. Operational Inefficiencies Unmanaged data can lead to inaccurate reporting and decision-making because it creates blind spots in your organization’s overall data landscape. 4. Extended Breach Impact Breaches involving shadow data are harder to detect and contain because IT teams often don’t know this data exists, prolonging response times and increasing costs. How Can You Shine a Light on Shadow Data? Preventing shadow data from being forgotten requires a proactive approach: Establish Clear Data Governance PoliciesDefine where and how employees should store and manage organizational data, ensuring these policies are communicated clearly. Educate EmployeesTrain staff on the risks of using unauthorized tools or storing sensitive information outside approved systems. Provide Approved ToolsOffer secure alternatives for file sharing and collaboration so employees don’t feel the need to use unsanctioned platforms. Conduct Regular AuditsPeriodically review your organization’s systems to identify unmanaged or unapproved data sources. Best Practices for Managing Shadow Data Hidden data probably already exists in your organization, here are some ways to manage it effectively: 1. Discover and Classify Data Use smart automated tools to scan your environment for unmanaged datasets and classify them based on sensitivity. 2. Assess Risks Evaluate the potential impact of each piece of shadow data if exposed or breached, focusing on securing high-risk datasets first. 3. Secure or Eliminate Bring important shadow data under formal management by migrating it into secure systems with proper access controls or securely deleting unnecessary files. 4. Implement Continuous Monitoring Adopt tools that provide ongoing visibility into your organization’s entire data ecosystem—including potential hidden sources. Why Should Organizations Care About Shadow Data? Organizations should care about hidden or forgotten data because ignoring it can lead to costly consequences: Data Breaches: Unsecured shadow data increases vulnerability to attacks. Regulatory Fines: Non-compliance with laws due to unmanaged shadow data can result in significant penalties. Reputational Damage: A breach involving sensitive customer information can erode trust with clients and partners. Wasted Resources: Storing unnecessary shadow data increases cloud costs and complicates IT management efforts. By addressing shadow data proactively, organizations can improve their security posture, reduce costs, and maintain compliance with industry standards. How C² Data Privacy Platform Can Help Managing shadow data doesn’t have to be overwhelming—this is where the C² Data Privacy Platform comes in. Our platform helps organizations identify, secure, and manage their sensitive information effectively: Comprehensive Data DiscoveryUsing advanced AI algorithms, our platform scans your entire environment—including cloud services—to uncover hidden shadow data. Automated Risk AssessmentThe platform evaluates the sensitivity of discovered datasets and provides actionable insights into potential risks. Centralized ManagementBring all your organizational data under one roof with our user-friendly interface that simplifies complex datasets management. Regulatory Compliance SupportThe C² Data Privacy Platform helps ensure compliance with major regulations by identifying non-compliant datasets and providing remediation recommendations. Continuous MonitoringStay ahead of future risks with real-time monitoring tools that alert you whenever new instances of shadow data appear in your environment. By leveraging the C² Data Privacy Platform, you can take control of your organization’s shadow data challenges while improving security, reducing costs, and maintaining compliance—all without adding extra complexity for your IT team. Shadow data may be hidden from view today, but ignoring it won’t make it go away. With the right strategies—and the right tools—you can shine a light on this hidden threat and enhance security across your organization. AWS Storefront
HIPAA Compliance in 2025: Advanced Strategies for Data Security and Privacy Management

As healthcare organizations face increasingly sophisticated cybersecurity threats in 2025, traditional approaches to HIPAA compliance are no longer enough. This article explores evolving strategies for maintaining HIPAA compliance through robust Data Security Posture Management (DSPM) practices that prioritize automation, scalability, and actionable insights. Evolving HIPAA Landscape and DSPM The updated HIPAA Security Rule in 2025 reflects the growing importance of advanced security measures to protect electronic Protected Health Information (ePHI). These changes emphasize the need for proactive data management and align closely with DSPM principles. Key updates include: Mandatory encryption for all ePHI at rest and in transit Enhanced multi-factor authentication to prevent unauthorized access Stricter requirements for risk analysis and vulnerability management Proactive and automated data discovery, classification, and risk assessment are critical components of any compliance strategy. Advanced DSPM Strategies for HIPAA Compliance Automated Data Discovery and Classification Automating the discovery and classification of ePHI across diverse environments is essential for comprehensive compliance. DSPM solutions leveraging AI can identify sensitive data across structured and unstructured sources, ensuring no critical information is overlooked. This reduces reliance on manual processes, minimizes errors, and provides a scalable approach to managing large datasets. Proactive Monitoring of Data Access Patterns Proactive analysis of historical data access patterns can provide valuable insights into potential risks. DSPM tools can flag unusual behaviors or anomalies by analyzing trends over time, enabling organizations to address vulnerabilities before they escalate into breaches. Automated Risk Assessment and Prioritization DSPM platforms excel in conducting automated risk assessments by identifying vulnerabilities across your data ecosystem. These tools assign risk scores based on the sensitivity of ePHI and its exposure level, helping organizations prioritize remediation efforts effectively without requiring constant manual oversight. Advanced Encryption Management Encryption remains a cornerstone of HIPAA compliance. DSPM solutions can integrate seamlessly with existing encryption technologies or provide built-in options such as: 256-bit encryption for robust data protection Format-Preserving Encryption (FPE) to secure sensitive data without altering its usabilityAdditionally, DSPM platforms should support complementary techniques like data masking, synthetic data generation, or redaction to further safeguard information. Comprehensive Data Lifecycle Management HIPAA requires careful management of ePHI throughout its lifecycle—from creation to secure disposal. DSPM solutions provide visibility into how data flows through your organization, ensuring compliance with retention policies while reducing unnecessary storage risks. Addressing Emerging Threats with DSPM AI-Driven Threat Detection Proactive DSPM tools can leverage AI-driven technology to identify patterns indicative of potential risks. By analyzing historical trends and automating alerts for suspicious activity, these tools help healthcare organizations stay ahead of evolving threats without requiring constant manual intervention. Managing Complex Cloud Environments As more healthcare providers adopt hybrid or multi-cloud infrastructures, managing ePHI across these environments becomes increasingly challenging. DSPM platforms simplify this process by providing centralized visibility into all data repositories—whether on-premise or in the cloud—and ensuring consistent application of security policies. Preparing for HIPAA Audits with DSPM HIPAA audits are becoming more rigorous in 2025, with increased focus on technical controls and documentation. DSPM solutions can streamline audit preparation by automating key tasks such as: Generating historical data on ePHI locations Documenting compliance activities like encryption practices and risk assessments Providing evidence of adherence to updated HIPAA standards By automating these processes, healthcare organizations can reduce the burden on staff while ensuring they meet audit requirements efficiently. Conclusion As HIPAA regulations evolve in 2025, healthcare organizations must adopt advanced strategies to stay compliant while protecting patient trust. Proactive DSPM practices—such as automated discovery, risk prioritization, and encryption management—offer a scalable path to achieving compliance. By leveraging these strategies, healthcare providers can not only meet regulatory requirements but also strengthen their overall security posture in an increasingly complex digital landscape. How C² Data Privacy Platform Can Help The C² Data Privacy Platform is essential for healthcare organizations navigating the evolving HIPAA compliance landscape in 2025. By automating the discovery and classification of sensitive data, the platform ensures that no critical information is overlooked, reducing the risk of breaches and non-compliance. Its advanced FIPS certified encryption capabilities align with HIPAA’s requirements for protecting ePHI, while the user-friendly interface simplifies risk management. With C², healthcare organizations can efficiently meet regulatory demands ad strengthen their overall data security posture in an increasingly complex environment. AWS Storefront
DSPM: Revolutionizing Data Security in the Cloud Era

In today’s rapidly evolving digital landscape, Data Security Posture Management (DSPM) has emerged as a critical solution for organizations grappling with the challenges of modern data protection. As data volumes expand and infrastructure becomes increasingly complex with hybrid cloud environments and multi-cloud deployments, traditional security models are no longer sufficient. DSPM offers a comprehensive, data-centric approach to security that addresses these challenges head-on. The Evolution of Data Security The traditional “Castle & Moat” strategy, which focused on restricting external access while trusting internal users, has become obsolete in the face of: Data migration to cloud environments Exponential growth in data volumes and unstructured data Fragmentation of data locations across diverse platforms Increased need for flexibility in access for remote workforces Enter DSPM: A Holistic Approach to Data Protection & Compliance DSPM extends protection beyond the traditional perimeter, securing sensitive data wherever it resides – on-premises data centers, in public cloud environments (AWS, Azure, GCP), or in SaaS applications (Salesforce, Microsoft 365). This comprehensive approach is crucial for meeting stringent regulatory requirements like GDPR, CCPA, HIPAA, and PCI DSS, and addressing data privacy concerns. Key Components of DSPM Automated Data Discovery and Classification: Continuous scans across all IT infrastructure to identify and classify data assets, including structured data and unstructured data, known and shadow data. Categorization of data based on sensitivity levels, data types, and compliance requirements to prioritize security efforts. Risk Assessment and Prioritization: Evaluation of current risk levels by data sources to identify data breach risks, assess data exposure, and focus on the most critical vulnerabilities requiring immediate attention. Efficient Remediation: Tools for quick implementation of security measures, including data encryption, data masking, and/or data tokenization. Integrates with existing data loss prevention (DLP) tools. AI-Driven Technology: Utilization of advanced Artificial Intelligence (AI) techniques, including Machine Learning (ML), Natural Language Processing (NLP), and Deep Learning (DL) for more accurate and efficient data protection. AI helps in the regular monitoring of data. Automation of surveillance identifies data at risk, resulting in action being taken and risk shut down. The Power of AI in Modern DSPM Modern DSPM solutions leverage various AI technologies, including: Machine Learning (ML): For automated data classification and anomaly detection Natural Language Processing (NLP): For analyzing unstructured data and understanding data context Pattern Matching: For identifying suspicious data access patterns and potential data exfiltration attempts Deep Learning (DL): For advanced threat detection and proactive risk prediction These AI-driven capabilities enhance the accuracy and effectiveness of data discovery, data classification, and risk assessment, allowing organizations to proactively identify and mitigate data security threats. Benefits of Implementing DSPM in Your Organization Elimination of inefficient manual processes and legacy data security solutions Improved resource allocation and cost savings Enhanced data security posture across all environments, including cloud environments and hybrid cloud architectures Better compliance with regulatory requirements and data privacy mandates Reduced risk of data breaches, data leaks, and data loss incidents By adopting Data Security Posture Management (DSPM), organizations can take a proactive stance in protecting their valuable data assets, mitigating data security risks, and ensuring data compliance, regardless of where their data resides. This proactive approach enables them to minimize the impact of potential cyberattacks and maintain customer trust and business continuity. How C² Data Privacy Platform Can Help The C² Data Privacy Platform empowers organizations to discover, secure, and manage sensitive data seamlessly across cloud and hybrid environments. Leveraging advanced AI and deep learning, it automates data discovery, classification, and risk assessment, reducing manual errors and improving efficiency. With built-in encryption and integration for masking and other security tools, the platform ensures adherence to regulations like HIPAA, GDPR, CCPA, SOX, PCI DSS, and GLBA. Its user-friendly interface provides actionable insights into exposure risks, enabling proactive data protection. By streamlining data security processes, C² helps customers mitigate breaches, maintain compliance, and build trust in an increasingly complex digital landscape. AWS Storefront
Do You Really Need a Cloud Security Audit?

In today’s digital world, cloud security audits have become commonplace to ensure robust data protection and compliance when moving from on-premise to the cloud. According to TechTarget, a cloud security audit is a periodic assessment of an organization’s ability to evaluate and document its vendor’s performance. These audits can be conducted internally or externally and are typically recommended at least once a year. But what exactly happens during a cloud security audit, and why is it so important? Let’s break it down. What Is Involved in a Cloud Security Audit? A cloud security audit is a comprehensive process designed to evaluate the security posture of your cloud environment. Below are the key areas typically covered during an audit: 1. Compliance with Industry Regulations and Standards Ensuring compliance with industry-specific regulations such as GDPR, HIPAA, or PCI-DSS is critical. Non-compliance can result in hefty fines and damage to your organization’s reputation. A cloud security audit verifies whether your organization meets these standards to avoid penalties and maintain trust. 2. Confidentiality, Integrity, and Availability of Data The audit assesses how well your organization protects sensitive data from unauthorized access (confidentiality), ensures its accuracy (integrity), and guarantees availability when needed. This evaluation ensures that data is handled responsibly and securely. 3. Current Security Controls Auditors review the effectiveness of existing security measures, such as firewalls, encryption protocols, and access controls. Weak or outdated controls can leave your organization vulnerable to breaches and regulatory penalties. 4. Risk Assessments Understanding your risk exposure is essential for building effective defenses. The audit identifies vulnerabilities in your cloud infrastructure and helps prioritize remediation efforts to strengthen your security posture. 5. Recommendations for Improvement No system is perfect, which is why audits often include recommendations for enhancing your security measures. These might involve implementing stricter access controls, improving monitoring systems, or adopting more advanced encryption methods. Preparing for a Cloud Security Audit: Proactive Steps While the audit process can seem overwhelming, being proactive can help ensure a smooth experience. Here are some actionable steps to prepare: 1. Identify Your Cloud Providers Create an inventory of all cloud providers in your ecosystem. Understanding their roles and purposes allows you to evaluate whether they align with your organizational objectives. Removing redundant or underperforming providers can reduce vulnerabilities. 2. Understand Shared Responsibility Models Cloud providers often operate under shared responsibility models where certain aspects of security are managed by the provider while others fall under your control. Clearly define: What the provider currently manages. What they could manage if necessary. What remains your responsibility. This clarity helps map out areas requiring additional protection on your end. 3. Review Access Controls Limit access to sensitive data by ensuring only authorized personnel have the necessary permissions. Implement role-based access control (RBAC), multi-factor authentication (MFA), and regular reviews of user access levels to minimize risks. 4. Encrypt Data at Rest and in Transit Encryption is one of the most effective ways to protect sensitive data from unauthorized access during storage or transmission. Ensure encryption protocols are consistently applied across all datasets. 5. Monitor Cloud Activity Establish baselines for normal activity within your cloud environment to detect anomalies quickly. Monitoring not only helps identify suspicious behavior but also catches human errors before they escalate into larger issues. 6. Keep Data Updated Regularly review the data stored in the cloud to identify outdated or unnecessary information that could pose risks. Cleaning up unused data improves efficiency while reducing potential attack surfaces. Why Cloud Security Audits Matter Cloud security audits are not just about meeting compliance requirements—they play a critical role in strengthening an organization’s overall security posture by: Identifying vulnerabilities before they can be exploited. Ensuring adherence to industry regulations. Enhancing customer trust by demonstrating commitment to data protection. Reducing long-term costs by proactively addressing risks. Conclusion A well-executed cloud security audit provides invaluable insights into the strengths and weaknesses of your organization’s cloud environment. By taking proactive steps—such as reviewing access controls, monitoring activity, and understanding shared responsibilities—you can ensure that your audit not only meets compliance requirements but also strengthens your overall cybersecurity framework.Cloud environments are dynamic and complex, but with proper preparation and continuous improvement, organizations can stay ahead of emerging threats while maintaining compliance with industry standards. This version avoids sales-heavy language while maintaining professionalism and providing actionable insights for readers. It also improves clarity through better organization with headings, bullet points, and concise explanations for each section. How C² Data Privacy Platform Can Help The C² Data Privacy Platform empowers organizations to discover, secure, and manage sensitive data seamlessly across cloud and hybrid environments. Leveraging advanced AI and deep learning, it automates data discovery, classification, and risk assessment, reducing manual errors and improving efficiency. With built-in encryption and integration for masking and other security tools, the platform ensures adherence to regulations like HIPAA, GDPR, CCPA, SOX, PCI DSS, and GLBA. Its user-friendly interface provides actionable insights into exposure risks, enabling proactive data protection. By streamlining data security processes, C² helps customers mitigate breaches, maintain compliance, and build trust in an increasingly complex digital landscape. AWS Storefront
What to Look for in a Sensitive Data Discovery Tool: A 2025 Guide

Sensitive data discovery is critical for organizations to protect their data, comply with regulations, and mitigate risks. However, selecting the right tool can be challenging. Here are the five key factors to consider when choosing a sensitive data discovery solution in 2025, optimized for modern needs like scalability, accuracy, and integration. Accuracy: Precision in Identifying Sensitive Data Accuracy is the cornerstone of effective data discovery. The tool you choose must: Distinguish between sensitive and non-sensitive data with minimal false positives or negatives. Leverage AI-driven models to analyze complex patterns and contexts. Ensure sensitive data is neither overlooked nor misclassified, which could lead to compliance risks or operational inefficiencies. Data Privacy: Ensuring Compliance and Trust Sensitive data discovery inherently involves scanning large datasets, which can raise privacy concerns. A robust tool should: Comply with global regulations like GDPR, CCPA, HIPAA, and PCI-DSS. Use encryption during scanning to protect sensitive information. Offer on-premises or hybrid deployment options for organizations with strict privacy requirements. Scalability: Handling Large and Growing Data Volumes As organizations generate more data across multiple environments, scalability is essential. Look for tools that: Support multi-cloud and hybrid environments seamlessly. Handle diverse datasets across structured, unstructured, and semi-structured formats. Scale efficiently without compromising performance or accuracy. Integration: Seamless Compatibility with Existing Systems A good sensitive data discovery tool must integrate smoothly into your existing tech stack. It should: Connect to various databases, cloud storage solutions, and SaaS platforms. Work with newer database technologies and legacy systems alike. Provide APIs for custom integrations and workflows. Cost: Balancing Investment with Long-Term Value Cost is always a concern, especially for large enterprises managing multiple data sources. The ideal tool should: Use AI-driven automation to reduce manual effort and operational costs. Offer flexible pricing models that align with your organization’s scale and requirements. Demonstrate measurable ROI by streamlining compliance processes and reducing risk exposure. Why Choose the C2 Data Privacy Platform? The C² Data Privacy Platform addresses all these key factors effectively: Accuracy: Uses AI-powered discovery to identify sensitive data with precision while minimizing false positives. Privacy: Ensures compliance with major regulations like GDPR, CCPA, HIPAA, and PCI-DSS through secure scanning methods. Scalability: Handles vast amounts of data across multi-cloud environments without performance degradation. Integration: Seamlessly connects to your existing systems, including cloud storage, databases, and SaaS platforms. Cost Efficiency: Automates the discovery process to save time and resources while prioritizing high-risk data for remediation. By leveraging the C² Data Privacy Platform, organizations can confidently address their sensitive data discovery needs while staying compliant, efficient, and secure in 2025’s ever-evolving digital landscape. AWS Storefront
The Limitations of Regex-Based Discovery in Data Security

Regex-based discovery faces significant challenges in modern data security: Limited Expressiveness: Struggles with complex patterns and context-aware data structures. Data Variability: Difficulty in creating patterns that capture all data variations accurately. False Positives: Rigid matching often leads to irrelevant or incorrect identifications. Maintenance Burden: Requires constant manual updates, time-consuming for large datasets. Performance Issues: Can be computationally expensive, especially for large-scale data analysis. Lack of Context: Unable to understand broader data context, leading to potential inaccuracies. Limited File Support: Only effective for text-based files, missing data in images or non-searchable PDFs. These limitations highlight why regex-based discovery alone is insufficient for comprehensive data security in today’s complex digital environments. How the C² Data Privacy Platform Can Help The C² Data Privacy Platform empowers organizations to discover, secure, and manage sensitive data seamlessly across cloud and hybrid environments. Leveraging advanced AI and deep learning, it automates data discovery, classification, and risk assessment, reducing manual errors and improving efficiency. With built-in encryption and integration for masking and other security tools, the platform ensures adherence to regulations like HIPAA, GDPR, CCPA, SOX, PCI DSS, and GLBA. Its user-friendly interface provides actionable insights into exposure risks, enabling proactive data protection. By streamlining data security processes, C² helps customers mitigate breaches, maintain compliance, and build trust in an increasingly complex digital landscape. AWS Storefront
PCI-DSS Compliance: Safeguarding Sensitive Data and Preparing for Audits
The Payment Card Industry Data Security Standard (PCI-DSS), established on September 7, 2006, is a critical framework designed to protect cardholder data. It applies to organizations like banks, healthcare providers, and any entity handling payment card information. Non-compliance can lead to significant penalties, making adherence essential for businesses. Why PCI-DSS Compliance Matters Compliance with PCI-DSS ensures the security of sensitive data such as credit card numbers, authentication data, and personal information. As organizations increasingly operate in cloud environments and handle vast amounts of data, understanding data sensitivity and vulnerabilities is fundamental to compliance. Achieving PCI-DSS compliance involves a comprehensive process that includes risk assessments, monitoring for malicious activities, updating documentation on data flows, and staying current with evolving standards. The PCI-DSS Audit Process A PCI-DSS audit is a thorough examination of your security infrastructure to ensure compliance with the standard. Here’s what the process typically involves: Focus on Sensitive DataAuditors review sensitive data elements such as primary account numbers (PANs), expiration dates, and routing numbers. They identify security gaps and may require remediation to address vulnerabilities. Recommendations for ImprovementAuditors often recommend preventive measures like documenting data flows, updating security policies, and improving access controls to protect cardholder data. Proactive PreparationThink of an audit as a health check-up for your organization’s security posture. Beyond addressing existing concerns, audits ensure proper documentation of sensitive data inventories and protective measures to mitigate risks in case of breaches. Preparing for PCI-DSS Compliance: Key Steps To streamline your audit process and minimize fines or penalties, take these proactive steps: 1. Achieve PCI-DSS Certification Certification requirements depend on transaction volume: Level 1 (6M+ transactions/year): Annual internal audits and quarterly PCI scans. Level 2 (1M-6M transactions/year): Annual risk assessments with Self-Assessment Questionnaires (SAQs) and quarterly scans. Certification involves a tailored risk assessment based on your transaction volume and cloud infrastructure. 2. Conduct Regular Risk Assessments Assess your IT assets and business processes for vulnerabilities. Document all systems involved in storing, processing, or transmitting cardholder data. Regularly update this inventory to reflect changes in your environment. 3. Implement Strong Security Measures Adopt measures such as: Encryption of stored and transmitted cardholder data. Robust firewalls to secure networks. Strong password policies to prevent unauthorized access. Continuous vulnerability monitoring and patch management. 4. Monitor Data Flows Ensure you have clear visibility into how cardholder data moves through your systems. This includes mapping out all connections between payment systems and other components in your network. Why Organizations Struggle with PCI-DSS Compliance Maintaining compliance requires significant investments in time, money, and resources. Challenges include: Managing complex cloud environments. Identifying sensitive data accurately. Keeping up with frequent updates to PCI-DSS standards. Ensuring scalability as transaction volumes grow. Moving Beyond Compliance: The Role of Technology Investing in advanced tools like AI-driven sensitive data discovery platforms can simplify the compliance process by: Automating sensitive data identification. Reducing false positives through context-aware analysis. Scaling seamlessly with growing datasets. Integrating easily with cloud-based storage systems. Final Thoughts PCI-DSS compliance is more than just a regulatory requirement—it’s essential for protecting customer trust and safeguarding sensitive financial information. By proactively preparing for audits, adopting robust security measures, and leveraging advanced technologies, organizations can ensure compliance while minimizing risks. How C² Data Privacy Platform Can Help The C² Data Privacy Platform empowers organizations to discover, secure, and manage sensitive data seamlessly across cloud and hybrid environments. Leveraging advanced AI and deep learning, it automates data discovery, classification, and risk assessment, reducing manual errors and improving efficiency. With built-in encryption and integration for masking and other security tools, the platform ensures adherence to regulations like HIPAA, GDPR, CCPA, SOX, PCI DSS, and GLBA. Its user-friendly interface provides actionable insights into exposure risks, enabling proactive data protection. By streamlining data security processes, C² helps customers mitigate breaches, maintain compliance, and build trust in an increasingly complex digital landscape. AWS Storefront
On-Premises vs. Cloud Data Privacy: Understanding Your Options for a Secure 2025
In today’s data-driven world, organizations grapple with a fundamental decision: Where should sensitive data reside? The choice between on-premise or cloud significantly impacts how you implement data privacy and security. Regardless of the path chosen, a commitment to robust security measures is non-negotiable. Both on-premise and cloud environments require adherence to stringent regulatory practices like auditing, role-based access control (RBAC), and continuous monitoring. However, the crucial first step remains the same: identifying sensitive data and assessing the associated risks. Without knowing where sensitive data resides and understanding its vulnerabilities, any data protection strategy is inherently flawed. The Core Challenge: Finding and Classifying Sensitive Data The biggest hurdle in modern data privacy is accurately locating and classifying sensitive data across the organization. This presents several challenges: Time-Intensive Process: The sheer volume of data in today’s businesses makes manual discovery impractical. Human Error: Relying on manual processes introduces the risk of overlooking sensitive data or misclassifying it, leading to vulnerabilities. Tool Limitations: Many traditional data discovery tools struggle to look beyond surface-level attributes, failing to analyze the contents of documents and other unstructured data sources. Overcoming these challenges is paramount to building a solid data privacy foundation. Navigating the On-Premise vs. Cloud Landscape When choosing between on-premise and cloud data storage, several factors must be carefully considered: Feature On-Premise Cloud Control Full control over infrastructure, security configurations, and data access. Shared responsibility model; control is distributed between the organization and the cloud provider. Security Requires in-house expertise to configure and maintain security measures. Relies on the cloud provider’s security measures, requiring careful evaluation of their security posture. Scalability Scaling requires significant capital expenditure and lead time. Offers on-demand scalability, but costs can fluctuate based on usage. Compliance Organizations are directly responsible for meeting compliance requirements. Cloud providers offer compliance certifications, but organizations are ultimately responsible for ensuring data is handled correctly. Accessibility Typically accessed via internal networks, limiting exposure. Accessible over the internet, requiring strong authentication and access controls. Cost High upfront capital expenditure, but predictable operating costs. Lower upfront costs but variable operating costs that depend on usage and storage volume. Data Governance Direct control over data governance policies and procedures. Requires careful configuration and oversight to ensure data governance policies are enforced. Disaster Recovery Requires investment in backup and recovery systems. Cloud providers offer built-in disaster recovery capabilities, but organizations need to ensure they meet specific RTO/RPO goals. Data Residency Data resides within the organization’s physical premises. Data may reside in different geographic locations, raising data sovereignty concerns. Expertise Requires internal expertise in infrastructure management, security, and compliance. Reduces the need for in-house expertise but requires a clear understanding of the cloud provider’s responsibilities. Increasingly, organizations are adopting hybrid cloud strategies to combine the benefits of both on-premise and cloud solutions. Understanding the specific needs and risk tolerance of your organization is essential in making the right choice. Building a Solid Data Privacy Framework Regardless of your infrastructure choice, the following steps are crucial for building a robust data privacy framework: Comprehensive Data Discovery: Implement a data discovery process that identifies all sensitive data, regardless of its location or format. Data Classification: Classify data based on its sensitivity level and regulatory requirements. Access Controls: Implement strict access controls to limit access to sensitive data to authorized personnel only. Data Loss Prevention (DLP): Deploy DLP solutions to prevent sensitive data from leaving the organization’s control. Encryption: Encrypt sensitive data both at rest and in transit to protect it from unauthorized access. Monitoring and Auditing: Continuously monitor data access and usage and conduct regular audits to identify potential security breaches. Training and Awareness: Educate employees about data privacy policies and best practices to foster a culture of security awareness. Incident Response: Develop a comprehensive incident response plan to handle data breaches and other security incidents. Moving Forward: A Proactive Approach to Data Privacy Protecting sensitive data is a complex and ongoing process that requires a proactive and comprehensive approach. By carefully considering your infrastructure options, understanding the challenges of data discovery, and implementing a solid data privacy framework, you can safeguard your organization’s data and maintain the trust of your customers. Rather than focusing on a specific product, this approach focuses on providing valuable information and insights, helping the reader make informed decisions about their data privacy strategy. How C² Data Privacy Platform Can Help The C² Data Privacy Platform empowers organizations to discover, secure, and manage sensitive data seamlessly across cloud and hybrid environments. Leveraging advanced AI and deep learning, it automates data discovery, classification, and risk assessment, reducing manual errors and improving efficiency. With built-in encryption and integration for masking and other security tools, the platform ensures adherence to regulations like HIPAA, GDPR, CCPA, SOX, PCI DSS, and GLBA. Its user-friendly interface provides actionable insights into exposure risks, enabling proactive data protection. By streamlining data security processes, C² helps customers mitigate breaches, maintain compliance, and build trust in an increasingly complex digital landscape. AWS Storefront
Can you meet compliance requirements on the cloud
Meeting compliance requirements is mandatory whether you’re storing data on-premise or in the cloud. If you’re in compliance with both, HIPAA, the Health Insurance Portability and Accountability Act of 1996, and CCPA, the California Consumer Protection Act, you’re most likely in compliance with the other US-specific compliances. The main international compliances are GDPR, the Global Data Protection Regulation, and LGPD, the Brazilian data protection regulation. How to meet compliance in the cloud Step 1: Identifying What Needs to Be Protected Many compliances are concerned with where and how consumer data are being stored. And understanding what is considered consumer’s data can be complex because it’s not limited to names, addresses, social security numbers, credit card numbers, and birth dates. Step 2: Add Your Protection The method of protection is up to your organization. Some organizations just require a firewall, some require keeping sensitive data on a VPN, and others require masking or encrypting. From our experience, organizations tend to like locking it down, encrypting, and masking. Step 3: Repeat It’s important to periodically run your identification process and continuously protect it because data may end up in the cloud, whether you know it or not. This process can be automated, giving the organization’s data privacy officer one less thang to do, but it’s heavily advised to take a look into the process to ensure that the whole process is working as it should. Step 4: Meet the Compliance As technology continues to be innovative, stay up to date with the compliance that applies to your organization because the organization can avoid hefty fines. How C² Discover can help C² Discover is your cloud-native sensitive data identifier. By connecting it to your relational database, NoSQL, data lakes, and data warehouses, C² Discover uses machine learning and AI technology to comb through your cloud data to identify all the sensitive data to meet compliance regulations and standards. Once the discovery is complete, the results go through to our user-friendly user interface. the interactive user interfaces present you with the views of your sensitive data from an overview to a granular view of a singular sensitive data element. At C² Data Technology, we believe in giving you insights into your cloud that turbocharge your data privacy mission.
Introducing Bias-Aware Machine Learning: A Paradigm Shift in Decision-Making

In the realm of machine learning, bias has always been a constant concern. Algorithms, though designed to assist in making decisions faster and more accurately, are not immune to biases. But fear not, because, at C² Data, we have revolutionized the landscape with our bias-aware machine learning models. Machine learning bias, as Tech Target elucidates, occurs when algorithms produce results that are inherently biased. This bias is often derived from the training process and the algorithm’s configuration. Let’s delve deeper into the different types of biases encountered: Algorithm Bias: Whether due to faulty algorithms or incompatibility with specific scenarios or software, this bias misinforms users, leading to erroneous outcomes. Sample Bias: The data used to train and test machine learning models may contain errors. Issues arise when the dataset is either too large, too small, or lacks diversity. Striving for the optimal balance in size and diversity is a challenge when testing the model. Prejudice Bias: Just like humans, machine learning models can develop prejudice bias based on the datasets reflecting inherent prejudices and stereotypes. Measurement Bias: Accurately measuring results demands meticulous attention. Any issues faced during this process can skew measurements, causing bias in the output. Exclusion Bias: Intentionally excluding certain data points can create skewness or bias within the machine learning model, undermining its efficacy. So, how does C² Discover come to your rescue? Carefully selecting and preprocessing the training data:At C² Discover, we have applied real-world schemas to generate synthetic data that perfectly matches real-world scenarios. This approach ensures that our training data remains representative and free from bias or outliers found within sensitive fields. Implementing fair and robust decision-making processes:Unlike traditional models, we incorporate a multi-model approach, amalgamating different models to make final decisions regarding sensitive data. By considering a broad range of perspectives, we ensure fairness and robustness in our decision-making process. Regularly evaluating the model’s performance:C² Discover continuously measures the performance of our models across various datasets. We meticulously evaluate outputs to pinpoint any potential sources of bias and make necessary adjustments to mitigate them. With C² Discover’s bias-aware machine learning, you can confidently embrace a paradigm shift in decision-making. Make informed choices without the shackles of biases that plague traditional algorithms. Embrace the future of machine learning today! Discover how our groundbreaking solutions can unlock the true potential of your data by clicking the button below.
Complying with Data Privacy Regulations

Ensuring Compliance with Data Privacy Regulations In today’s data-driven environment, protecting sensitive information is crucial. C² Data Technology provides solutions to the significant challenges businesses face in adhering to data privacy regulations. Our objective is to provide you with the necessary tools and expertise to effectively navigate this intricate landscape. Data privacy regulations play a vital role in safeguarding individuals’ personal information, whether they are EU citizens, residents of California, or holders of financial and health data, from threats like data breaches, malware, ransomware, and more. Despite having robust policies in place, the risk of breaches remains. It is essential for organizations to have a clear understanding of the location of their sensitive data, which may be found in unexpected places beyond traditional storage locations. At C² Data Technology, we specialize in offering solutions that provide comprehensive visibility into your data ecosystem. Our advanced technologies empower you to identify and safeguard sensitive data wherever it may be, ensuring compliance and enhancing your overall security posture. By partnering with us, you not only gain peace of mind but also the confidence to innovate and thrive in today’s data-driven economy. Allow us to guide you through the intricacies of data privacy and security so that you can concentrate on what truly matters—your business’s success and earning the trust of your stakeholders. Introducing C² Data Privacy Platform Presenting the C² Data Privacy Platform—a robust solution designed to provide organizations with unparalleled visibility into the location of sensitive data across the entire enterprise, along with advanced data protection measures. C² Manage Access comprehensive visibility into all data regions within your AWS account with C² Manage. This capability forms a solid foundation for extensive data discovery, answering the critical question: “Where is my data stored?” Efficient management of AWS accounts also enables cost optimization, enhancing operational efficiency. C² Discover Utilizing state-of-the-art technologies such as machine learning, AI, and contextual knowledge, C² Discover excels at identifying sensitive data across various enterprise data connections. It meticulously locates sensitive data, even in the most remote corners of your data ecosystem. C² Secure Employing advanced technologies such as machine learning, AI, and contextual knowledge, C² Discover excels at identifying sensitive data across diverse enterprise data connections. It meticulously locates sensitive data, even in the most remote corners of your data ecosystem. A Comprehensive Regulatory Solution For a fool-proof approach to compliance initiatives, apply precise roles and policies to protect your data, ensuring seamless adherence to regulations. At C² Data Technology, we grasp the complexities of modern data environments. Our C² Data Privacy Platform enables organizations to navigate these challenges with assurance. Gain clarity, ensure compliance, and reinforce your data security strategy with C² Data—your proactive partner in comprehensive data privacy management. Moreover, our platform connects you with legal professionals and privacy experts specializing in data protection. Their expert guidance guarantees that your organization achieves full compliance, reduces legal risks, and strengthens your overall data governance framework. Selecting C² Data means empowering your organization with robust data privacy solutions to thrive in today’s dynamic regulatory landscape. At C² Data Technology, we firmly believe that complying with data privacy regulations goes beyond a mere checkbox exercise—it’s an opportunity to demonstrate your dedication to customers and their privacy. Prioritizing data privacy not only upholds ethical standards but also enhances your organization’s reputation. Do not allow data privacy regulations to overwhelm you. Embrace the journey with us at C² Data Technology. Let C² Discover become your trusted partner along the way. Request a demo today and witness how our powerful tools can enhance your data privacy compliance efforts. Together, we can establish a more secure and trustworthy digital future.
Find Your Risk, Protect Your Data

In today’s complex corporate data landscape, complexity arises from the multitude of applications and teams needing access to data. This often leaves organizations uncertain about the location of their sensitive data and consequently, unaware of the risks they face in terms of compliance with regulatory standards. Our Comprehensive Solution Introducing the C² Data Privacy Platform, a robust solution designed to empower organizations with clear visibility into the whereabouts of sensitive data across the entire enterprise. C² Manage With C² Manage, users gain comprehensive visibility into all data regions within their AWS account, establishing a solid foundation for thorough data discovery. This capability directly addresses the fundamental question: “Where is my data stored?” Additionally, C² Manage enables cost optimization through efficient AWS account management. C² Discover Powered by advanced techniques such as machine learning, AI, and contextual knowledge, C² Discover excels in identifying sensitive data across various enterprise data connections. It precisely pinpoints the exact locations where sensitive data resides, even in less visible areas of your data ecosystem. C² Secure Ensuring data security is a top priority, and C² Secure offers a range of robust options including encryption, masking, synthesis, and redaction. With over 21 years of experience serving Fortune 500 clients, C² Secure provides the assurance that sensitive data is effectively safeguarded. With the C² Data Privacy Platform, organizations can confidently navigate the complexities of modern data environments. Enhance compliance, gain clarity, and strengthen your data security strategy with C² Data – your proactive partner in data privacy management.
Who Has Access to Your Cloud Data

Choosing a cloud service and setting it up for your company can feel daunting. You might wonder: Can I trust this cloud provider with my sensitive information? What security measures do they have in place? Who is able to access the data stored in the cloud? Concerns about cloud security and data protection are valid for everyone. Nobody wants their private information shared without permission. Fortunately, there are steps we can take to safeguard our data in the cloud. Who Can Access Your Cloud Data Regardless of the cloud service you select, there are only three groups with access: the Cloud Access Security Broker (CASB), your company, and the people you choose to grant access to. A Cloud Access Security Broker (CASB) acts as a gatekeeper between the customer and the provider of cloud services. They implement the organization’s security policies and ensure compliance with regulations whenever someone accesses data on the cloud. Once you have a cloud service, your company decides who can access it through authorized logins and the provider controls access as well. Be Proactive About Cloud Data Security There are many proactive steps we can take at individual, company, and cloud levels. Individuals Use a password for cloud access and change it every three months Log out after finishing your cloud session Avoid public networks when accessing the cloud Limit downloads on the server Company Review internal policies Secure all devices Implement multi-factor or two-factor authentication Enforce strict role permissions Cloud Regular backups Keep an eye on upgrades Secure your data Pay attention to overseas servers Introducing the C² Data Privacy Platform The C² Data Privacy Platform is a powerful solution for managing and securing data in cloud and hybrid environments. It simplifies data management, discovery, and security. Key Features: C² Manage: Get complete visibility into all data areas within your AWS account, laying the groundwork for better data discovery by answering the key question: “Where is my data located?” Turn off unnecessary accounts to save on AWS costs. C² Discover: Use advanced data discovery techniques like machine learning, AI, and contextual knowledge to accurately analyze and find sensitive data across various sources, including relational databases, NoSQL, Data Lakes, and Data Warehouses. C² Discover gives you a clear view of data locations, pinpoints areas with sensitive information, and assigns risk scores based on the types and amounts of sensitive data found. C² Secure: Protect your sensitive data with recommendations on encryption, masking, synthesis, and redaction. With over 21 years of experience working with Fortune 500 clients, C² Secure ensures your important data is well protected.
Do All Clouds Have the Same Data Protection?

Companies are moving to the cloud because it’s cheaper to store files, it’s flexible, and it allows users access regardless of where they are located. There are four types of clouds, private, public, hybrid, and multi-cloud. Based on the type of cloud, the level of security varies. Private Cloud and Cloud Protection A private cloud is a server that allows hardware and software resources that be controlled and addressed by one user. That means that it’s owned by a user and receives the most security since the owner can customize the infrastructure. However, it comes at a substantial cost because it gives you maximum control over what goes in, what comes out, how it’s protected, and who has access. Public Clouds and Cloud Protection Public clouds are on-demand servers for organizations and individuals who can gain access to the cloud through the Internet. This makes them owned by a public cloud service provider. This type of cloud requires the users to rely on themselves and the cloud service provider for protection. Hybrid Clouds Protection A hybrid cloud is a combination of computing environments, public clouds and private clouds, and on-prem and cloud data centers. This is because some applications in the IT ecosystem are run on computing, storage, and services in a variety of environments, resulting in the protection heavily relying on third-party applications and you. The users would have to rely on themselves. Multi-Clouds and Cloud Protection Multiclouds use two or more clouds to achieve different tasks. This allows the user to complete a task while taking advantage of the benefits and functionality of the different clouds. As the other clouds discussed, the security responsibility is on the user. Regardless, of the data protection level and who provides the protection, knowing your exposure and your risk level is something that always needs to be known. Meet the C² Data Privacy Platform The C² Data Privacy Platform is your powerful, all-in-one solution for managing and securing data across enterprise cloud and hybrid environments. It handles data management, discovery, and security with ease. Key Features: C² Manage: Gain full visibility into all data regions within your AWS account, laying the foundation for comprehensive data discovery by answering the crucial question: “Where is my data stored?” Turn on and off the unnecessary accounts to reduce AWS costs. C² Discover: Leverage cutting-edge data discovery techniques, including machine learning, AI, and contextual knowledge, to accurately analyze and identify sensitive data across various sources in various data sources, relational databases, NoSQL, Data Lakes, and Data Warehouses. C² Discover provides a unified view of data locations, highlights areas with high concentrations of sensitive information, and assigns the risk scores based on what types and how much sensitive data was found. C² Secure: Protect your discovered data with expert recommendations on encryption, masking, synthesis, and redaction. With over 21 years of experience serving Fortune 500 clients, C² Secure ensures your sensitive data is effectively safeguarded.
Finding Sensitive Data

At C² Data Technology, we aim to find sensitive data in places where it’s not obvious. Practically, we seek to locate and classify sensitive entities in your data repositories. Using machine learning, we detect over 35 types of sensitive data, covering the bases for HIPPA, PII, and national and international regulations using machine learning. This post will focus on what makes C² Discover the next-generation tool to detect and monitor sensitive data. What Is the Common Approach to Detecting Sensitive Data? The most common approach is rule-based, as it relies mainly on hand-crafted rules with a foundation in regular expressions. Rules can be designed based on domain-specific labels and syntactic-lexical patterns. Regex can work well with the lexicon is exhaustive. However, it’s impossible to cover all patterns due to domain-specific rules and incomplete dictionaries. Take entity “address” for example. It’s next to. Impossible to include all patterns for varied address formats around the work and it relies heavily on manual effort to construct. Regex’s don’t work when the data doesn’t follow any known rules! How Does C² Discover Develop a Next-Generation Solution? By tapping into the breadth and depth of machine learning algorithms and innovative cloud technologies, C² Data came up with a hybrid Machine Learning model. We call our solution C² Discover’s exclusive Deep Learning based model. It uses a combination of machine learning resources powered by AWS (e.g., AWS Comprehend) and additional layers of contextual rules based on our experience. The results based on these combined methods provide a higher degree of accuracy than either one alone. How does C² Discover Detect Sensitive Data? Reducing the Human Effort Traditional rule-based approaches require a considerable amount of engineering skills and domain expertise. Applying deep learning-based models, on the other hand, is effective in automatically learning representations and underlying factors from raw data. C² Discover will save significant effort in designing rules and writing regex expressions as well as adapting quickly to new data environments. Employing Rich Features in Model Training By sourcing synthetic data based on the real-world schema, we were able to build C² Discover’s exclusive learning-based model. We incorporated not only world-level and character-based representation learned from an end-to-end neural model, but also additional information (e.g., gazetteers and linguistic dependency). These rich features allow our model to have a better understanding of different data repositories. Applying Weighted Results By combining different resources results, C² Discover’s robustness is guaranteed. In this way, bias can be hugely decreased by using C² Discover than other solutions that depend on one model only.
Are Cloud Providers Responsible for All Aspects of Data Security?
What Is a Cloud Provider Cloud providers are third-party companies that offer a cloud-based platform, infrastructure, application, or storage services. Their responsibilities typically cover the following: Certifications and standards Technologies and service roadmap Data security, data governance, and business policies Service dependencies and partnerships Contracts, commercials, and SLAs (Service Level Agreements) Reliability and performance Migration support, vendor lock-in, and exit planning Business health and company profile Cloud Providers and castles have many similarities. They both host and have a standard protection system, like keys and locks, doors, a moat, etc. The responsibility falls on the users and the royal family that is using them. Like any attacker on a castle, talented hackers can get into the infrastructure at any time. The entire system is ruined if they don’t protect what’s inside. How Can the C² Data Privacy Platform Help? The C² Data Privacy Platform is your all-in-one solution for managing and securing data across enterprise cloud and hybrid environments. It handles data management, discovery, and security with ease. Key Features: C² Manage: Gain full visibility into all data regions within your AWS account, laying the foundation for comprehensive data discovery by answering the crucial question: “Where is my data stored?” C² Discover: Leverage cutting-edge data discovery techniques, including machine learning, AI, and contextual knowledge, to accurately analyze and identify sensitive data across various sources. C² Discover provides a unified view of data locations, highlights areas with high concentrations of sensitive information, and assigns the risk scores based on what types and how much sensitive data was found. C² Secure: Enhance your data security posture and mitigate the impact of breaches. With over 21 years of experience serving Fortune 500 clients, C² Secure offers expert recommendations on data encryption, masking, synthesis, and redaction to effectively protect sensitive data.
Can Cloud Data Be Controlled?

Are you looking at all the different ways to store data in the cloud, but want to know about data privacy and security? A data lake may be the answer. What Is a Data Lake? A data lake is a designated location where you can store, process, and secure substantial amounts of knowledge in all forms from structured, semi-structured, and unstructured. Enterprises like to use it to either: ingest or process data. Some great benefits include: Improve security and governance Lower total costs of ownership Simplify management Prepare to incorporate AI and machine learning Speed up analytics How Can the C² Data Privacy Platform Help? The C² Data Privacy Platform is your all-in-one solution for managing and securing data across enterprise cloud and hybrid environments. It handles data management, discovery, and security with ease. Key Features: C² Manage: Gain full visibility into all data regions within your AWS account, laying the foundation for comprehensive data discovery by answering the crucial question: “Where is my data stored?” Turn on and off the unnecessary accounts to reduce AWS costs. C² Discover: Leverage cutting-edge data discovery techniques, including machine learning, AI, and contextual knowledge, to accurately analyze and identify sensitive data across various sources in various data types, structured, unstructured, and semi-structured. C² Discover provides a unified view of data locations, highlights areas with high concentrations of sensitive information, and assigns the risk scores based on what types and how much sensitive data was found. C² Secure: Enhance your data security posture and mitigate the impact of breaches. With over 21 years of experience serving Fortune 500 clients, C² Secure offers expert recommendations on data encryption, masking, synthesis, and redaction to protect sensitive data effectively.
Challenges of Machine Learning-Based Data Discovery
Machine learning looks at the actual data values rather than trying to match metadata or specific strings and therefore it is much more accurate than regex. In fact, many data discovery tools claim to use machine learning when combing through data environments, looking for sensitive data. However, it may face several challenges. Data Bias and Fairness Machine learning models are sensitive to biases present in the training data. If the training data contains biased or unrepresentative samples, the model can learn and perpetuate the biases, leading to unfair or discriminatory outcomes. Ensuring fairness and mitigating bias in machine learning models is a critical challenge. Data Privacy and Security Machine learning models often require access to sensitive or private data. Protecting the privacy and security of such data. Protecting the privacy and security of such data during training and deployment is essential. Adversarial attacks, data breaches, or unintended information leakage can pose significant risks. Data Processing and Cleaning Preparing the data of machine learning often involves data preprocessing, including handling missing values, outliers, and inconsistent formatting. These tasks can be time-consuming and require domain knowledge and expertise. Interpretability and Explainability As models become more complex, their interpretability and explainability diminish. Understanding and interpreting the decision made by a model can be challenging, which can hinder trust and acceptance, particularly in critical domains such as healthcare or finance. Lack of Transparency The models can be viewed as black boxes, making it difficult to understand their internal workings. This lack of transparency can lead to skepticism and resistance, especially in scenarios where explainability is required, such as regulatory compliance or auditing. Data Quantity and Quality Machine learning models typically require large amounts of high-quality labeled data for effective training. However, obtaining labeled data can be very expensive, time-consuming, and in some cases, practically infeasible. Limited or low-quality data can adversely affect model performance and generalization. Model Robustness and Adversarial Attacks Machine learning models can be vulnerable to adversarial attacks, where malicious actors intentionally manipulate inputs to mislead or exploit the model. Ensuring robustness against such attacks is crucial, especially in safety-critical applications like autonomous vehicles or cybersecurity. Addressing these challenges requires a comprehensive and thoughtful approach, encompassing data collection and preprocessing practices, model selection and training, robust evaluation methodologies, and ethical considerations throughout the entire machine learning pipeline. How Is C² Data Privacy Platform’s Data Discovery Different C² Discover’s data discovery methods don’t rely on machine learning only. C² Discover leverages AI, contextual knowledge from our extensive experience protecting Fortune 500 companies, and machine learning to deliver accurate data discovery results. Our “data first, metadata second” approach ensures direct data analysis, using surrounding data to confirm and enhance our findings right out of the box. Understand what was found using the interactive, drill-down user interface. C² Discover displays the landscape of where the risk lies throughout the environment through the sensitive data landscape. Drill down to the source level to see what and where the highest concentrations of sensitive data are. The percentage breakdown is also displayed for users to view.
Cloud Security, Do You Need It?

The cloud stores data in a remote location that is accessed via the internet so you can share your files and data, and has some built-in ways to protect your data: Back up your data to the cloud No need for external hard drives Remotely update and sync your files Share your files easily Remote work made easy Keep your files encrypted Cloud Security The cloud provider’s job isn’t just to house the data of companies, it’s to also ensure the cloud users how safe it is. When developing the cloud, they focused on: user and device authentication, data and resource access control, and data privacy protection. To achieve optimum security, they start with secure access control, zero-trust network, change management, web application firewall, data protection, and continuous monitoring. 6 Pillars of Cloud Security Secure Access Control: secure Identity Access Management (IAM) protocol; access to what they need and that’s all Zero-Trust Network Security Controls: separating the data from what needs to be protected and what doesn’t Change Management: management has control over governance and compliance when there is a request; can catch any suspicious activity Web Application Firewall: added protection to add a blockade to breachers à serves as an indicator of suspicious behavior Data Protection: strongly encourage encrypting files and have a plan of what to do if there is suspicious activity and breach Continuous Monitoring: comparing to older logs and auditing Let’s Get in the Mind of the Hackers The object of the game is you must get money or something that will lead to the money like credit card information, social security, someone’s identification, etc. Before, they relied on pickpocketing and scamming scenarios to get quick cash. With everything becoming digital, added tactics like phishing emails and malware to get your information. Two common events happen: they get access to the data and expose known data that isn’t fictionalized, or they expose data that you didn’t know residing in the cloud that wasn’t fictionalized. What You Can Do No matter what you do to your cloud security process, hackers are going to try to get their paycheck. Here are things we can do to add to the existing security protocol: Move sensitive data off the cloud Encrypt sensitive data Change your passwords Require 2-factor authentication/multifactor authentication Invest in firewalls on email servers Educate yourself and the company to make sure Know what information is on the cloud How Can C² Discover Help? The C² Data Privacy Platform is your all-in-one solution for managing and securing data across enterprise cloud and hybrid environments. It handles data management, discovery, and security with ease. Key Features: C² Manage: Gain full visibility into all data regions within your AWS account, laying the foundation for comprehensive data discovery by answering the crucial question: “Where is my data stored?” Turn on and off the unnecessary accounts to reduce AWS costs. C² Discover: Leverage cutting-edge data discovery techniques, including machine learning, AI, and contextual knowledge, to accurately analyze and identify sensitive data across various sources in various data types, structured, unstructured, and semi-structured. C² Discover provides a unified view of data locations, highlights areas with high concentrations of sensitive information, and assigns the risk scores based on what types and how much sensitive data was found. C² Secure: Protect your discovered data with expert recommendations on encryption, masking, synthesis, and redaction. With over 21 years of experience serving Fortune 500 clients, C² Secure ensures your sensitive data is effectively safeguarded.
The Problem with Regex-Based Discovery

Unlocking the Potential: Exploring the Limitations of Regex-based Data Discovery In today’s increasingly data-centric landscape, regex-based discovery serves as an essential methodology for effective pattern recognition and data extraction. Regular expressions, or regex, are powerful tools that allow users to search for specific strings within vast datasets, simplifying tasks that might otherwise be time-consuming or nearly impossible. However, it is crucial to recognize the inherent challenges and limitations associated with its application. While regex can be remarkably efficient for certain types of data patterns, it can also become unwieldy, especially when dealing with complex data structures or nuanced variations in the text. Understanding these limitations is vital for maximizing the potential of regex while effectively navigating its challenges.
C² Discover 3.0 released Sensitive Data Landscape
Today we are excited to announce some major advancements to the C² Discover product that provide users with a deeper understanding of their sensitive data across the enterprise. This includes a new Sensitive Data Landscape, Improved Data Risk Monitoring, Improved Discovery Performance, and Extended File Support. Sensitive Data Landscape This feature shows your data exposure risk across all your data sources. Based on our proprietary risk scoring algorithms the sensitive data landscape shows you what types of sensitive data are stored in your databases and files as well as the potential risk it represents. The goal is to provide insight into your enterprise’s risk so you can determine how best to protect your data. C² Discover calculates risk by analyzing the data discoveries you have run as well as how many other data sources you have but have not yet scanned. C² Discover tells you what types of sensitive data you have such as personal identifiable data, financial data, and healthcare or HIPAA data. Improved Data Risk Monitoring Get even closer and see how your risk is trending over time. C² Discover shows if your sensitive data increased, decreased or stayed the same on a monthly, quarterly, or annual basis. This tells you when and where to act to secure your data before it is too late. Improved Discovery Performance With C² Discover 3.0, the scanning process has been made smarter so you get your results faster. C² Discover already provided sophisticated sampling features to allow you to control how you search for your sensitive data. Some of our larger clients asked us to improve the speed of the Discoveries for large or complex databases as well as hundreds or even thousands of data sources. We listened and improved how C² Discover does parallel sampling. One more step to making C² Discover the best solution for large enterprises! Smarter File Support Large customers have legacy systems that use older file types. C² Discover now supports EDI files, both X12 and EDIFACT and can discover sensitive data in individual worksheets in Microsoft Excel (XLS, XLSX). C² Discover scans all your files and has built-in intelligence to identify common industry file types to improve the accuracy of the results. C² Discover is your enterprise-level cloud solution. C² Discover connects to your cloud-native data sources, whether it’s relational databases, NoSQL, S3, data lakes, or warehouses, and discovers sensitive data. Our approach to sensitive data discovery uses our deep learning technology, utilizing machine learning models and contextual knowledge based on our unmatched experience with data privacy experience. Visually understand your risk across your enterprise, what and where the sensitive data was found.