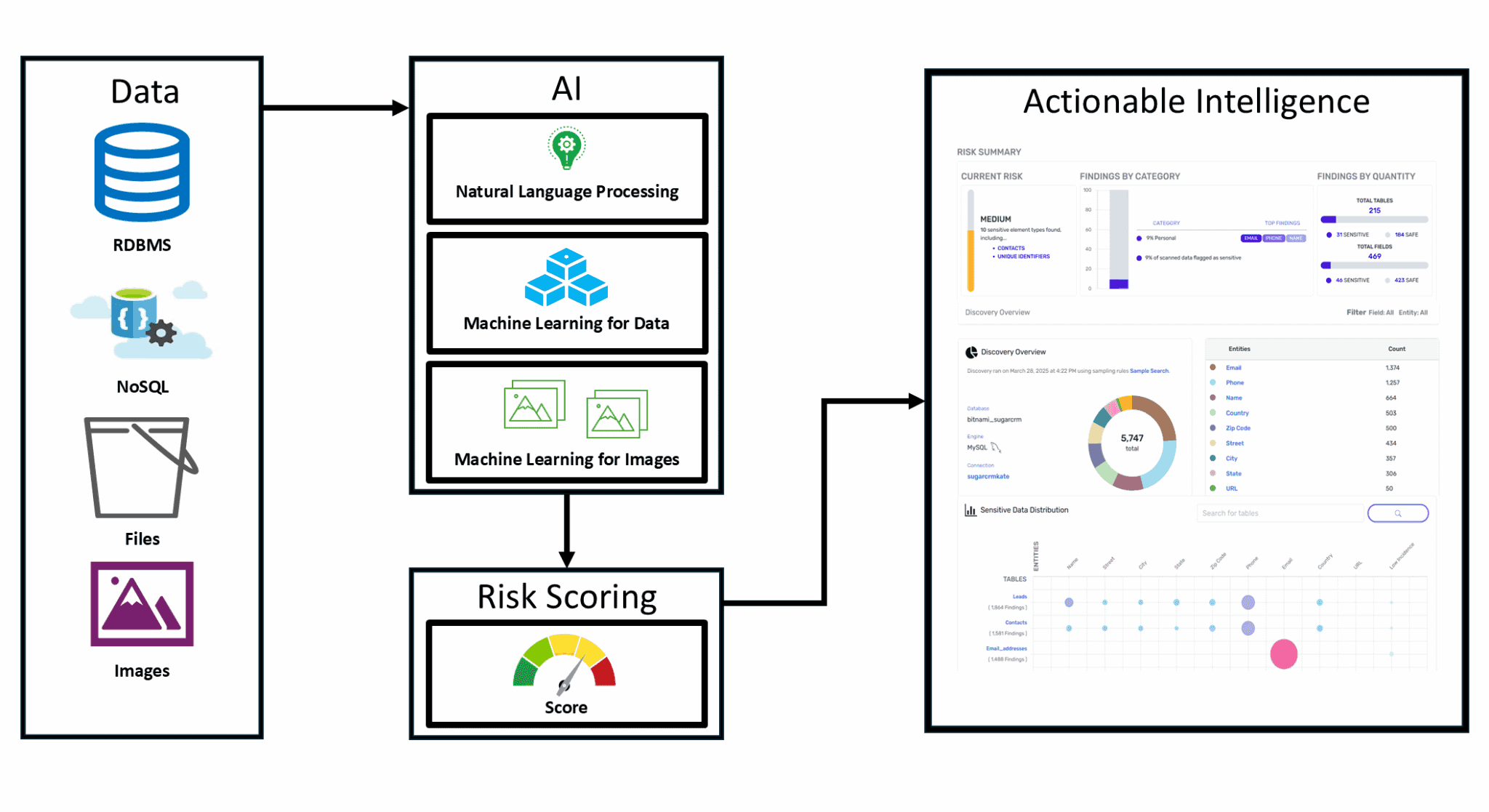
You Can't Protect What You Can't See
The C² Data Privacy Platform uses AI to automatically discover, secure, and manage sensitive data across your entire environment — before a breach, audit, or regulatory fine forces your hand. Built for security and compliance teams in healthcare, financial services, telecom, and beyond.

Trusted by leading organizations to protect their most sensitive data
Unlike rule-based scanners, C² uses natural language processing and machine learning to understand data in context — identifying sensitive fields in RDBMS, NoSQL, files, and images, then scoring risk automatically so your team knows exactly where to act.
Three Reasons Security Teams Choose C²
Key Capabilities

Michael Logan
Recovering operator turned data evangelist. Two decades wrangling regulated data sets, cloud migrations, and grumpy auditors. Builder of products that let enterprises move fast on AI without waking up in front-page breach headlines. Still believes the right privacy architecture can turn “no” into “now” for the business.
CEO

George Barroso
Career-long systems whisperer who never met a legacy database he couldn’t tame. Spent 25+ years stitching together security, privacy, and performance in environments where downtime is not an option. Lives at the intersection of architecture diagrams and incident runbooks, making sure sensitive data stays visible to the right people and invisible to everyone else.
CIO

Kris Glover
Hands-on architect with a bias for shipping secure-by-design systems, not just slideware. Veteran of large-scale cloud deployments where sensitive data hides in all the places scanners forget to look. Part machine-learning tinkerer, part threat-modeling purist, dedicated to building an AI-driven privacy platform that actually keeps up with how fast your engineers ship code.
Principal Architect
See Your Sensitive Data Risk in 15 Minutes
Book a demo and get a live walkthrough of your data landscape — or get started instantly on AWS Marketplace.